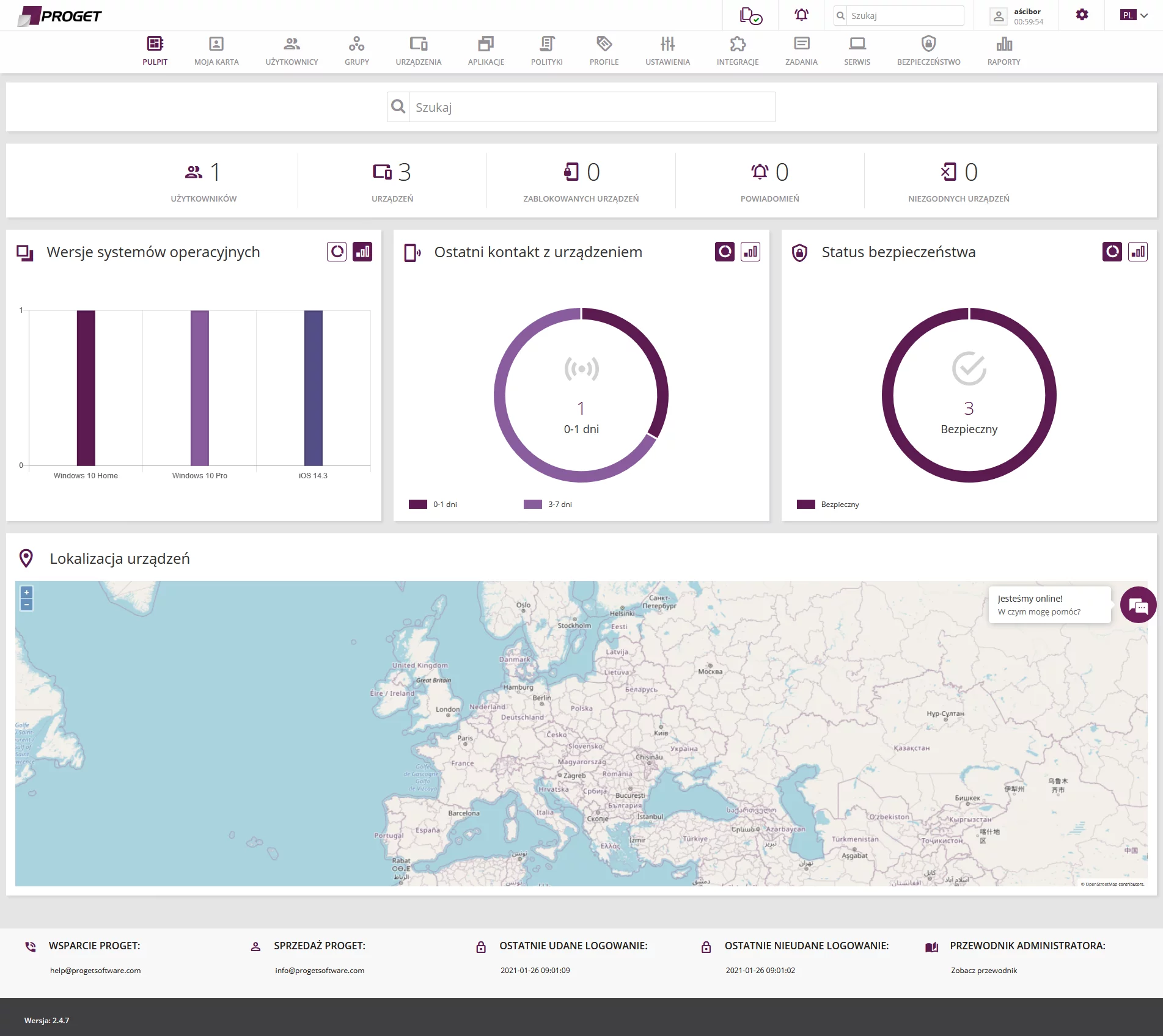
At remote work, but not only! And it does not matter where employee’s device is physically located. The further away from the employer, the better because protection of corporate data on a managed device (remotely or from the office) is the essences of software by Polish company Proget Software. Compatriots-programmers and their bosses can make good and stable software. Maybe that is why Proget as the MDM and EMM class product takes the form of specialized one? If it were in the Gartner square, it would probably be placed as a player who pays particular attention to the specific part of the market. Obviously, it has its advantages.
The following analysis of Proget solution is sponsored by Proget Software.
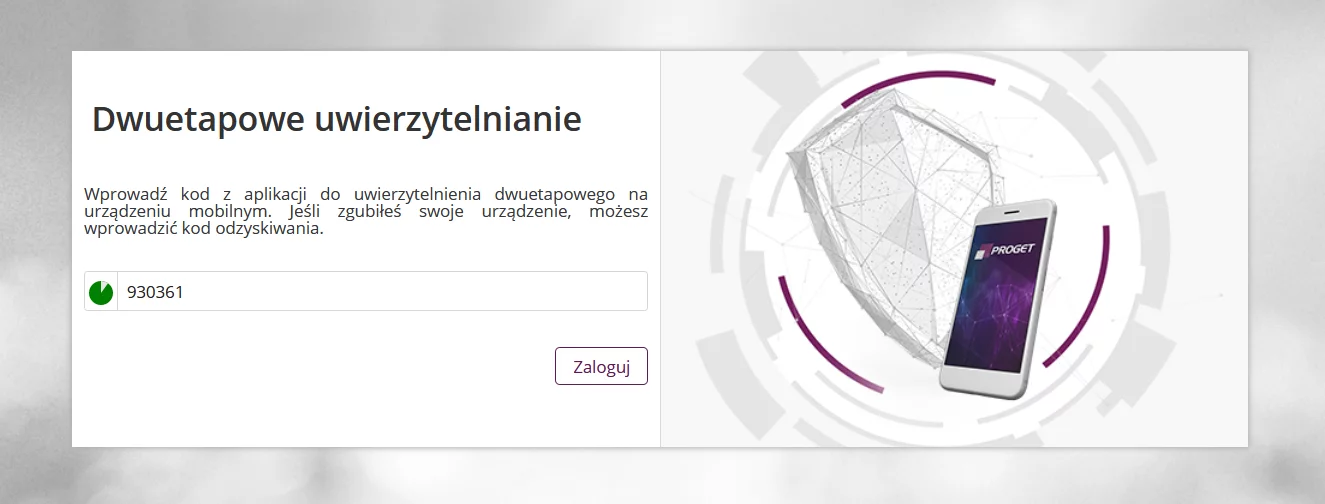
Proget does not attempt to pretend to be a product which it is not. And that is good. It has many features for remote management of systems and applications, so the first contact with the software can be one of its kind. The console immediately puts an administrator on standby, telling him: You will not install Proget in the standard way! It is worth to read the documentation that provides good guidance: from the way of securing login into the console (2FA + trusted IP addresses of administrators) to deploying and discussing all elements in the dashboard. And there are many settings after logging. It is good we have a manual, phone and email support.
Proget Software step by step
We have tested the product according to the following methodology. This allowed us to assess control and management capabilities of Proget, and it turned out that the solution was included on the list of recommended IT solutions for the SMB and Enterprise market by AVLab. Add to that pre- and after-sale support (also in English), as well as technical support from software engineers. Finally, we get a solid basis for sales outside our country.
The Proget Software cooperation with distributors and partners around the world shows that the solution has a stable position to enter new markets. That is good because Proget can positively surprise. This is the MDM (mobile device management) class solution, and at the same time it fits into the MAM (mobile application management) class product, as well as EMM (enterprise mobility management). So a station of desktop or server type is not a limitation for Proget. We can implement this software not only on a mobile, but also on a laptop, all-in-one computer, and a server.
We have taken into account the following criteria when evaluating the product:
- Is the solution easy to install? How to fast we can install it on multiple devices?
- Apart from Polish, what other languages are supported? How quickly does technical support respond to a call? How can Proget engineer solve a problem?
- Does the software have sufficient number of features for remote management?
- How long does it take to synchronize data on devices, and what is actually available for synchronization?
- How to separate corporate applications and files from private data? To what extent is it possible?
- What does the security policy offer for mobile devices and desktops? Does settings allow to secure access to a device well enough?
- Does the software have a mechanism to prevent stealing or transmitting from a device (something like so-called Data Leak Prevention)?
Ad1. Installation of the EMM / MDM system of Proget
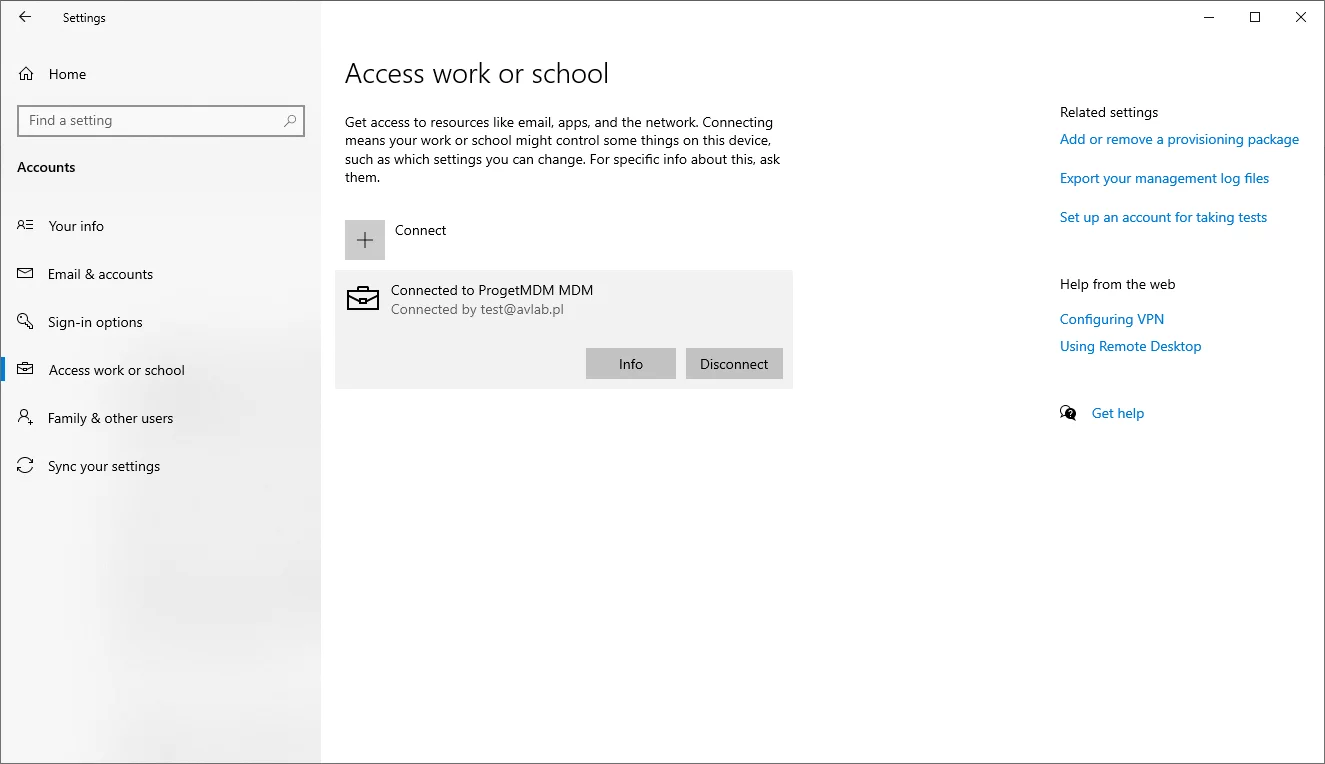
Agentless deployment is implemented on Windows workstations (optional agent will be soon available for Windows devices, later on, it will become mandatory). This means that we did not install a traditional application in the tested version – for Windows, we set up a console connection by providing a login and password in the work account registration zone.
Proget integrates with Active Directory which simplifies mass deployment in a workspace. In addition, it offers support for email servers of Microsoft Exchange, Lotus Domino, ActiveSync protocol, and platforms of Android Enterprise, Samsung Knox, and Apple Business Manager. A wide range of technologies ensures that all devices are added to the console. The operating manual is well described. And of course, technical support is available via phone, email, chat, and remote connection with a support engineer in case of any problems.
Proget should be deployed in each workstation and mobile device through the technologies mentioned above. Alternatively, you can send an email with the installation instruction to employees. The system will send such message if we configure the SMTP connection with the corporate mail server. This is very easy, and thus an employee will be sure that he receives email from corporate domain that does not attempt to impersonate the organization.
Ad2. Help and customer support in other languages
A website presents developer’s portfolio in three languages: Polish, English, and Russian. The console is also available in German and Romanian. Diversity is important because Proget Software cooperates with distributors and partners around the world. The software is sold, among others in Germany, Russia, India, Romania, Ukraine, Hungary, and Kazakhstan. App for smartphones is available in Polish, English, German, Russian, and Romanian.
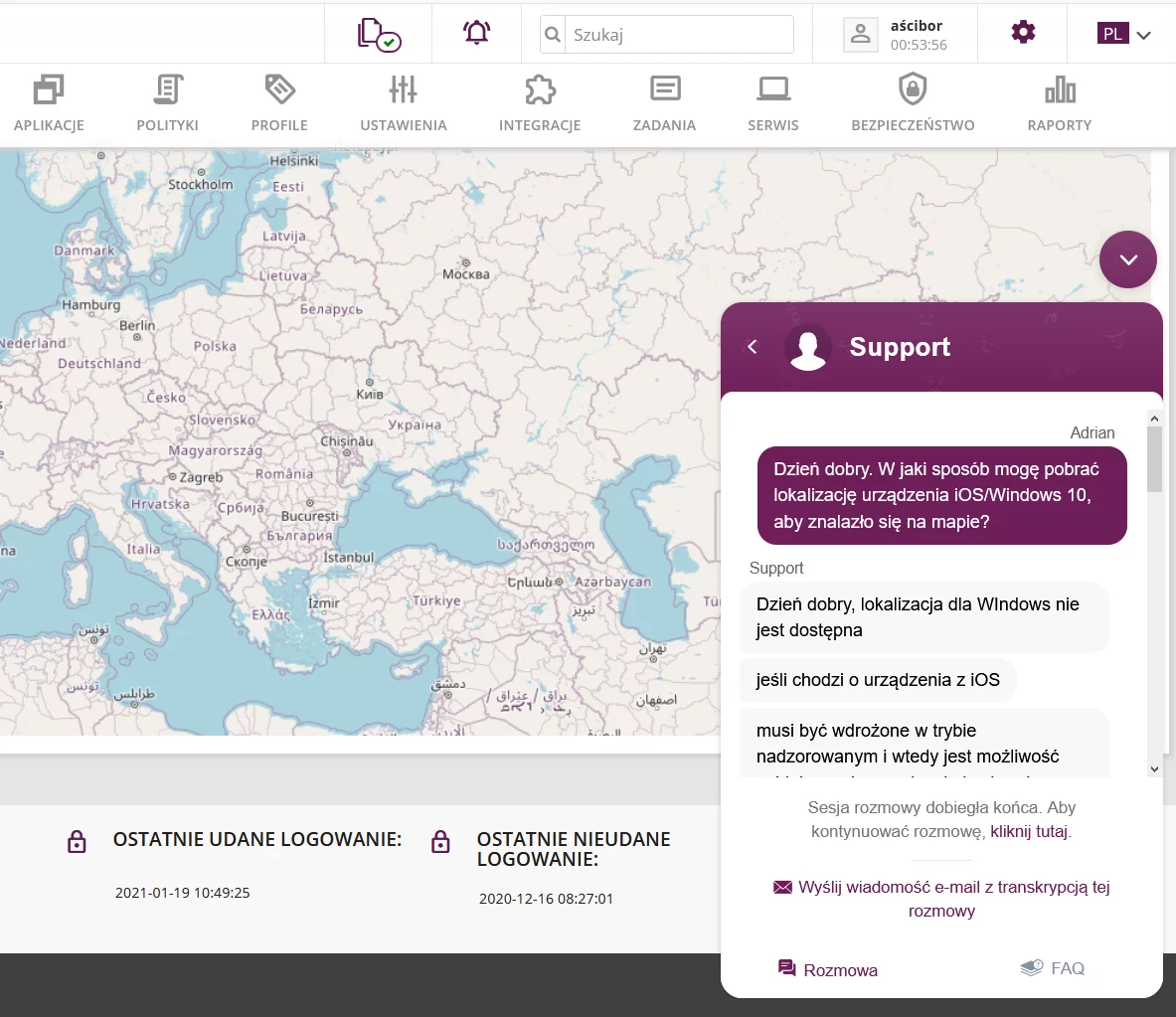
Technical support in Poland is provided in native language and English. Chat is available from the administrator console – Proget Software responds very quickly to all questions. In the same window, the communication system allows to start a conversation or share desktop with an engineer without installing additional applications. The entire conversation history is sent to an email address with all the details.
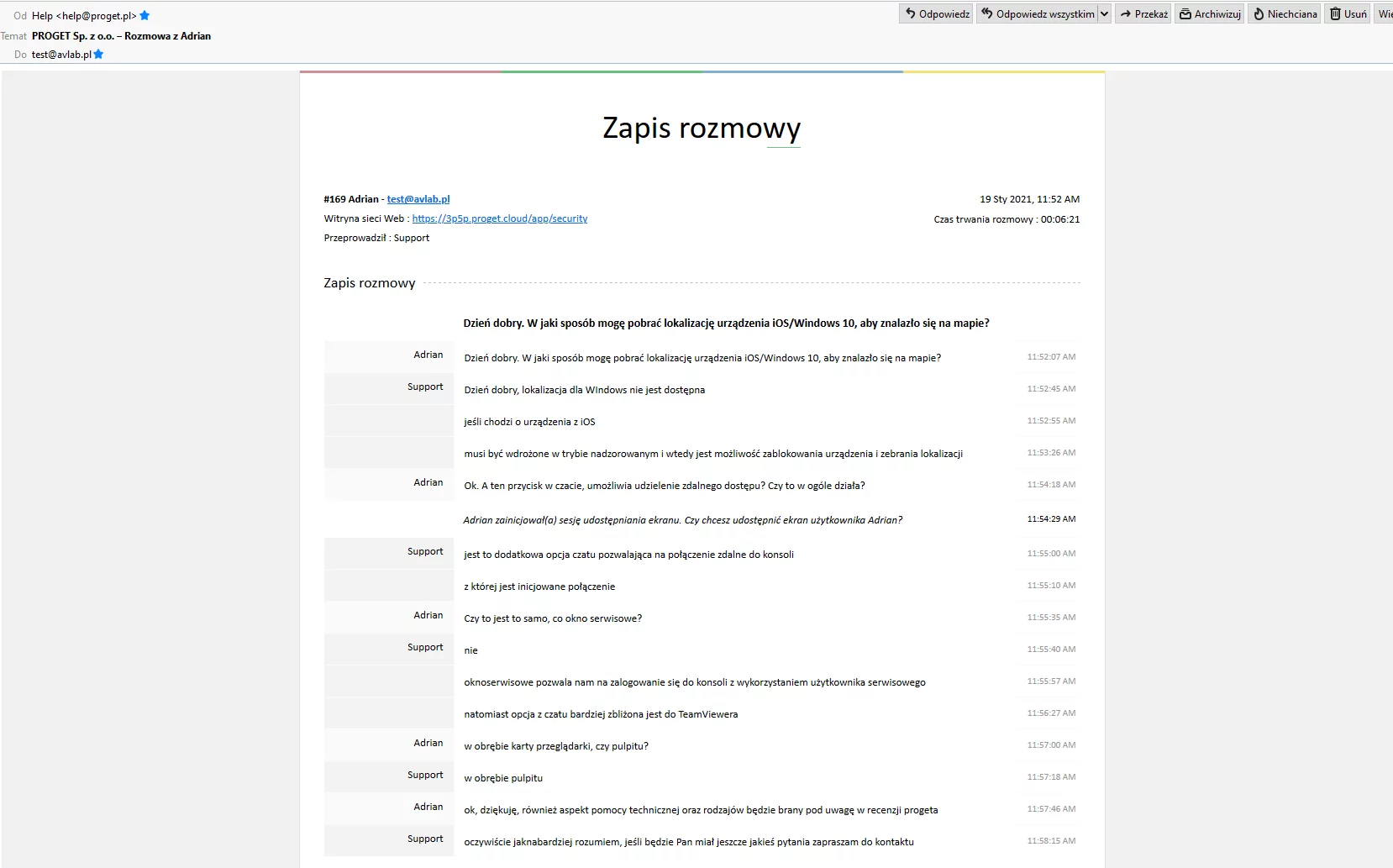
The ticket system is based on Polish and English languages, applies to all countries, and also significantly simplifies international problem solving (or individual integration with requirements of the end user). Basic problems and technical issues are immediately explained, or potentially several minutes after the question is asked. Sometimes a few hours of waiting for a response is also a possible scenario. In emergency situations, we can call and enable a special service mode in the console. An expert will be able to see settings, find a malfunction, and help with the configuration.
With unexpected problems which we have been able to generate, slightly more complicated cases can be forwarded to the development team. However, we should not be afraid of difficult and individual deployment because Proget developers can design a unique feature, such as hiding applications from the smartphone screen that are not relevant when we are driving a vehicle. A helpful feature in the implementation for German company was to block access to the Internet in specific countries in order not to bear the costs of employee’s phone unnecessarily. The implementation of the Proget individual system has been carried out for Reinert Logistics with a fleet of over 750 vehicles and employing over 1000 professional drivers.
We summarize technical support as follows: Proget engineers provide support at a higher than basic level. They do it well, quickly and efficiently. We evaluate this company very highly for the time they take to solve problems, and for various ways of communication with a team of employees from Proget Software.
Ad3. Remote management of devices
Proget System supports Windows, Android, and iOS. There are some differences in remote management of these systems, although they result mainly from architectural limitations. So the mobile system is designed to remotely control Wi-Fi, VPN, Bluetooth, locations, files, containers, kiosk, etc. For Windows, the configuration is limited (all features are described in the documentation).
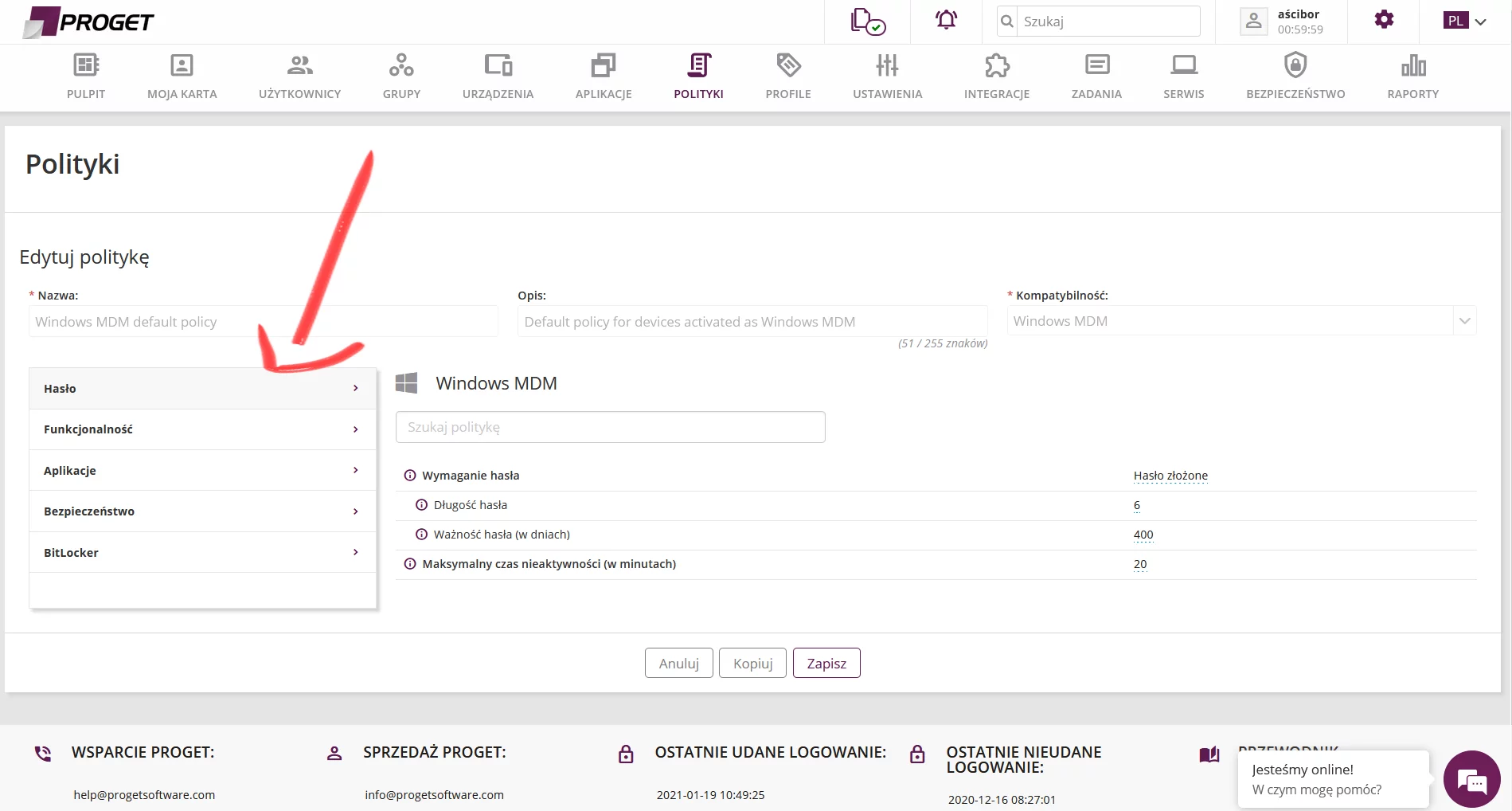
In the policy for Windows we can find support, among others, for:
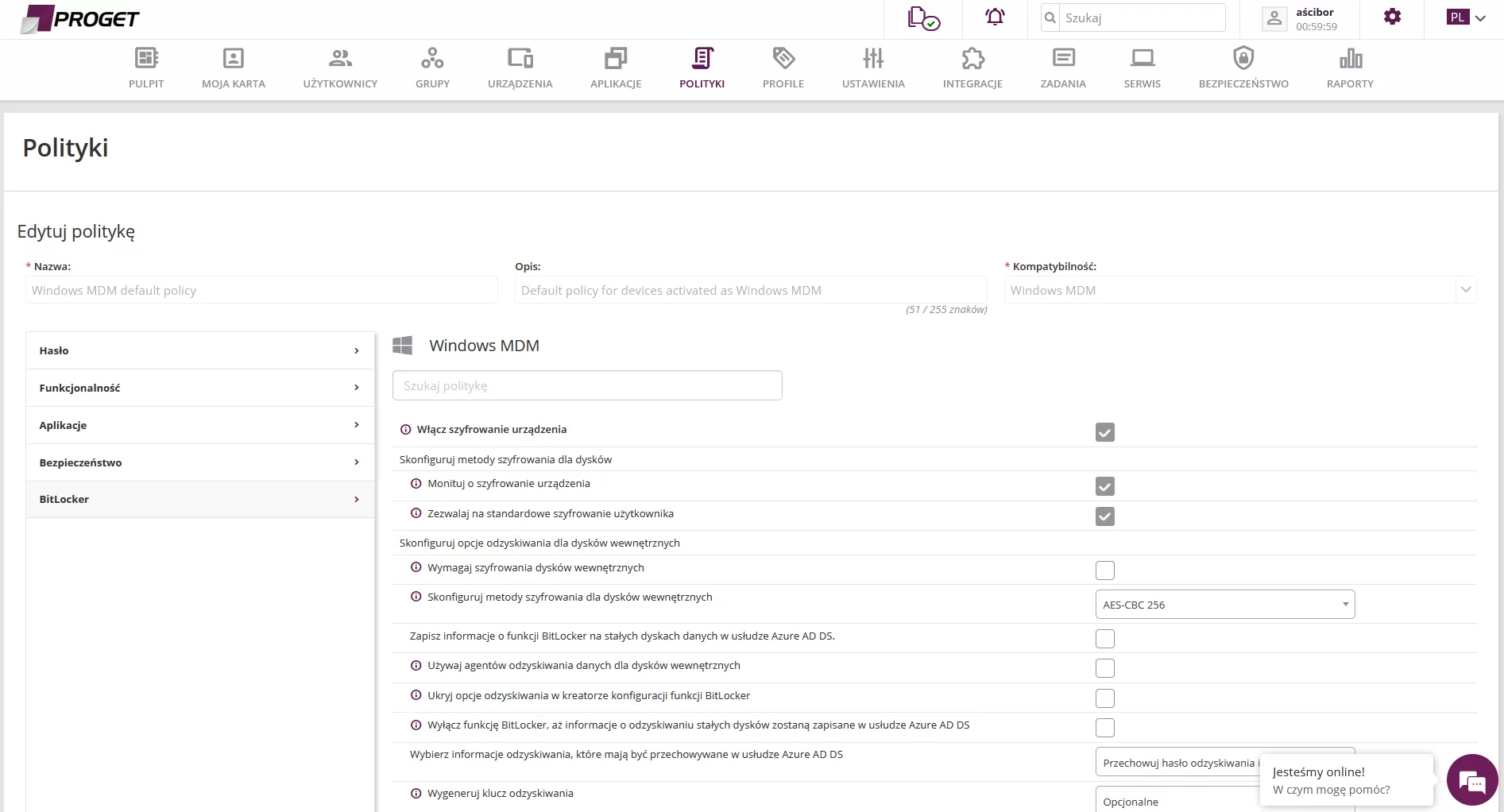
- BitLocker disk encryption with and without TPM (Trusted Platform Module), including a selection of encryption algorithm.
- Configuration of the password reset method.
- Factory reset of Windows.
- Friendly policy for creating login passwords for the system.
- And few other minor settings.
The biggest disadvantage for Windows policy is the lack of support for configuration of web resources with corporate files. Of course, Windows environment provides much better solutions for businesses and access management to shared network resources. You can also use an external solution to share encrypted files and chat among employees.
We have confirmation from Proget that the console is systematically and slowly expanding to meet business requirements. Support for MacOS will be provided soon.
Other features will be discussed in the field of supported mobile business solutions: Samsung KNOX, iOS, Android, Android Enterprise. Only using it with Android and iOS shows the full potential of the solution.
Here we can find settings such as:
- Monitoring device security by detecting known vulnerabilities and potentially dangerous actions such as: enabling developer mode, USB debugging, detecting root account, etc.
- Smartphone can automatically connect to a wireless network if it is within range.
- Saving device location at specific time intervals, e.g. every few hours.
- Importing necessary certificates and business contacts from VCF file to employee’s devices.
- Uploading corporate files and documents to the Proget console which will be shared with each employee in the smartphone app.
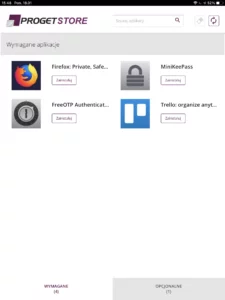
- Configuration of corporate applications installed from the store or a file. Such software may be mandatory to install, i.e. a smartphone will do it for you.
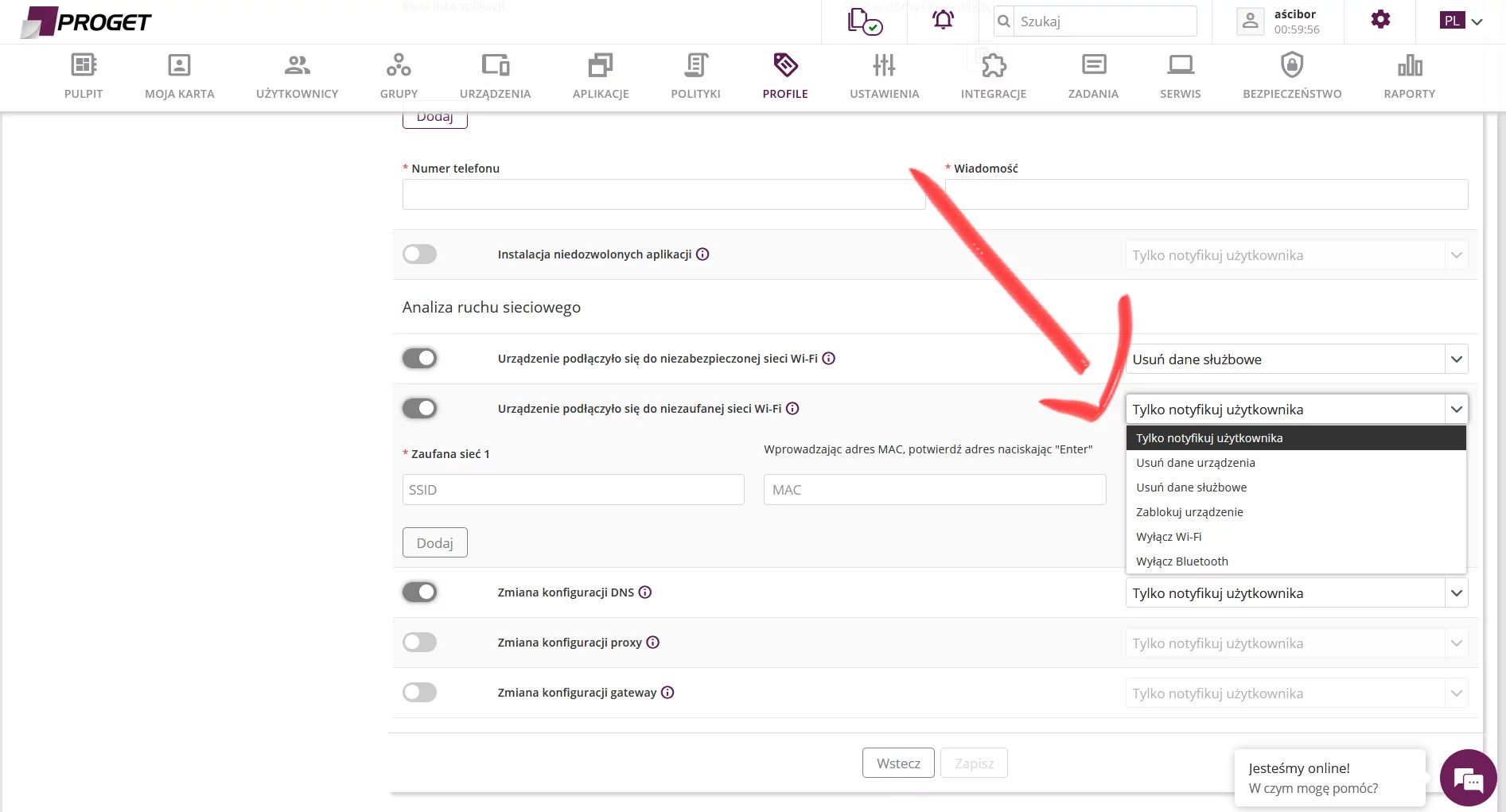
- Responding to an action, such as connecting to an unsecured wireless network or leaving a designated zone according to GPS transmitter. This will cause a smartphone to trigger a defined action, for example, it will remove business data or lock the screen (which can be protected by an additional policy: password, fingerprint, iris, or face scanner, etc.):
Of course, there are more similar settings, and the full potential of Proget Software can be best experienced on specific implementation examples. Only then it will be possible to realize how many elements can be configured.
Of course, not every policy can be assigned to a given operating system. For example, Apple smartphones are more restrictive as regards user’s privacy, Android smartphones give more freedom on this matter, and for Windows, the configuration is symbolic.
Ad4. Synchronization and intervals of downloading data
Changes in settings of groups, policies, applications, the Microsoft Exchange server, etc. are transferred to a device according to the default interval in the so-called “push” mode. For managed devices (Active Directory, ActiveSync, Lotus Domino), we can define the time interval for downloading new emails, contacts, calendar events, for example, every few minutes, hours, once a day, or immediately (push).
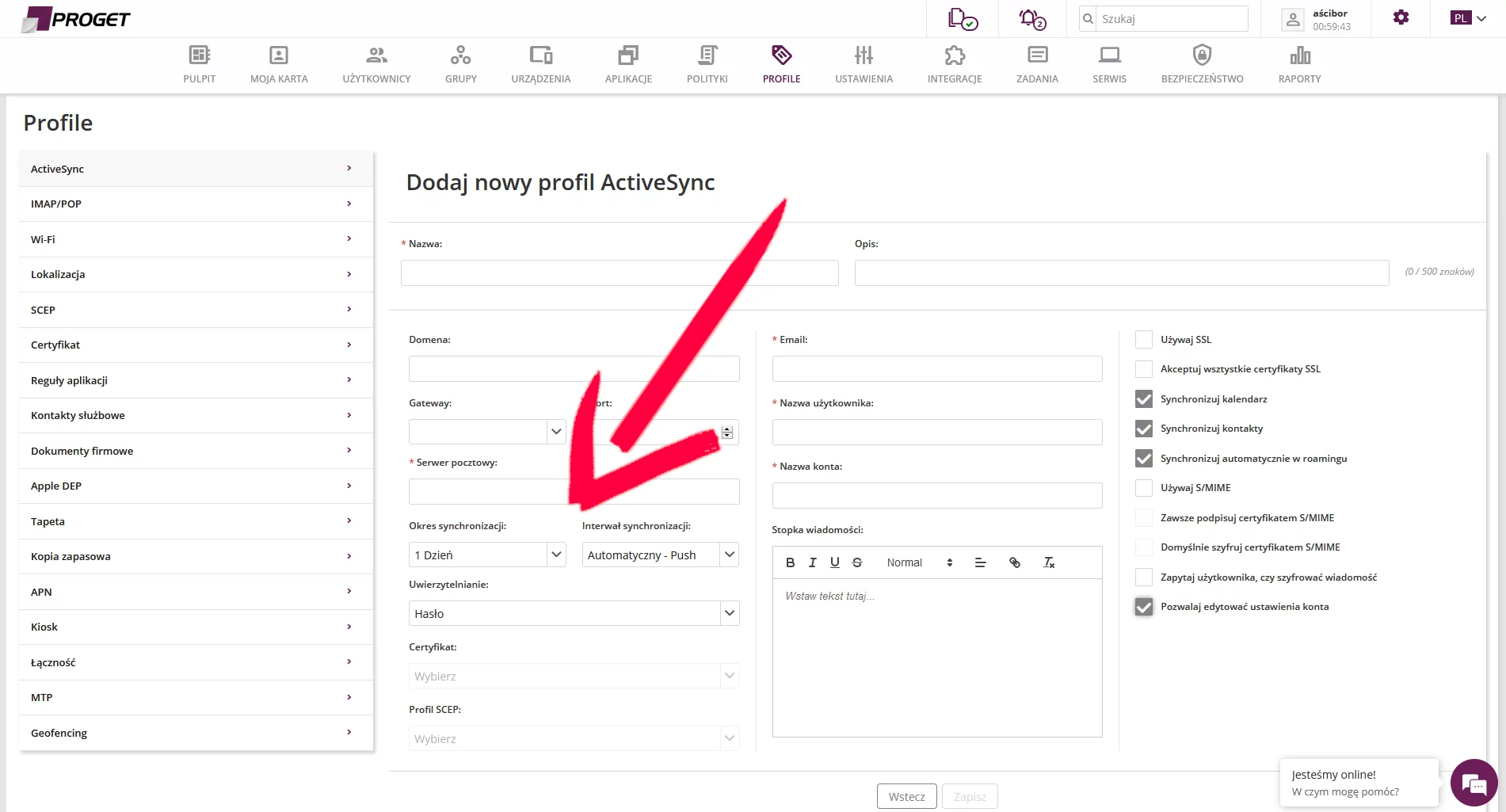
We did not have any problems with almost immediate automatic changes on a mobile device because the default mode (push) downloads data and implements new settings with no additional administrator interference. The synchronization interval settings in fact depend on the organization’s individual requirements, also on mobile phones in roaming – outside the country.
Ad5. Corporate applications and documents, and personal files
The administrator can select applications (from a file or from Google Play, App Store) that will be installed on an employee’s device. In addition, some of them can be automatically configured with appropriate parameters. This prevents situations in distributed environments where there is a need for manual configuration or to provide an employee with instructions.
Freedom is so high that we can assign policy to a specific GPS location. Then the device will recognize that this is company “site” and propose appropriate settings.
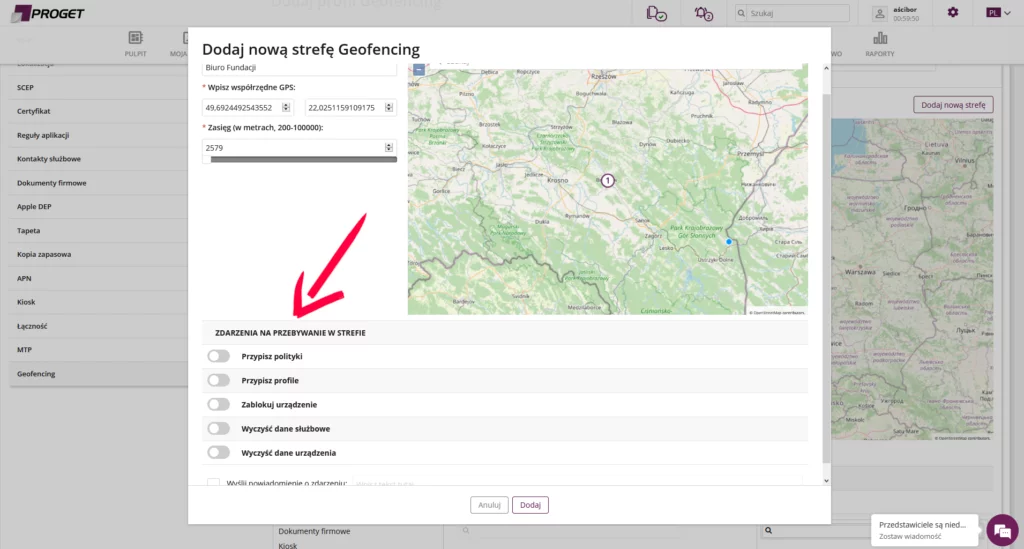
If an employee leaves a designated zone, he will obtain greater privacy and control of the device. The use of devices by employees within the meaning of “Bring Your Own Device” has also flaws because a smartphone brought to a company may be infected, have an old version of the operating system. The Proget agent installed on the device cannot interfere in everything. Sometimes even basic security cannot be achieved without support of the smartphone producer, so devices that are no longer supported should be regularly replaced.
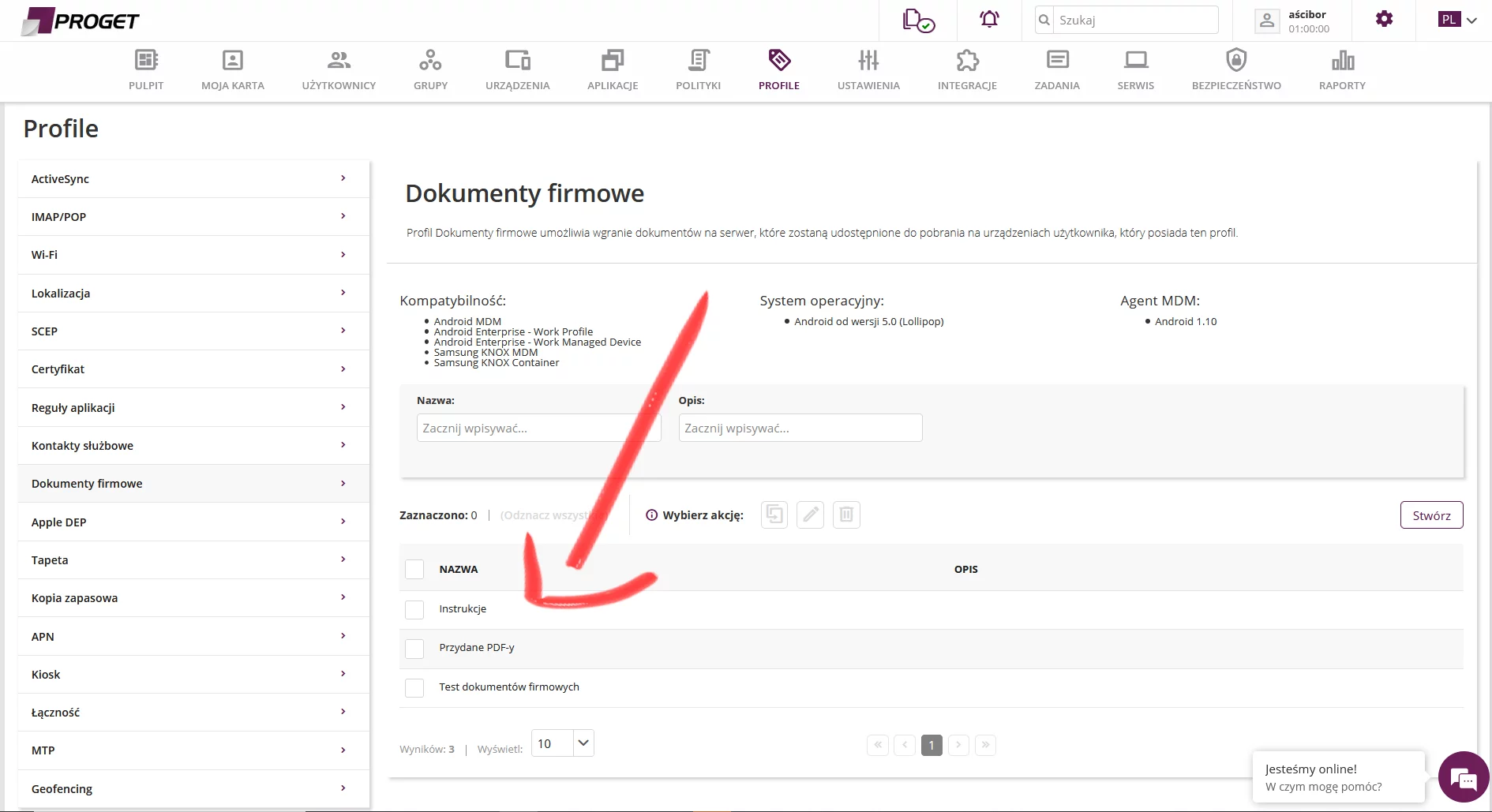
The configuration responsible for corporate documents is modest. The administrator sends a folder or files to the Proget console. This way, the data will be available for download on devices. For group work only one setting for “corporate documents” is not enough. We will treat it rather as access to copies of corporate files such as reports, excel files, summaries, manuals, etc..
Ad6. Securing devices
Let us start with protection of Windows workstations. The security policy includes password logging. Previous settings introduced by the device owner, such as fingerprint or face scanning using Windows Hello, will be overwritten by a less secure method – a password to which the administrator may impose the required number of characters, as well as the expiry date of that password. This is not an error in Proget. Simple, the Windows API does not allow full access to the system to such extend.
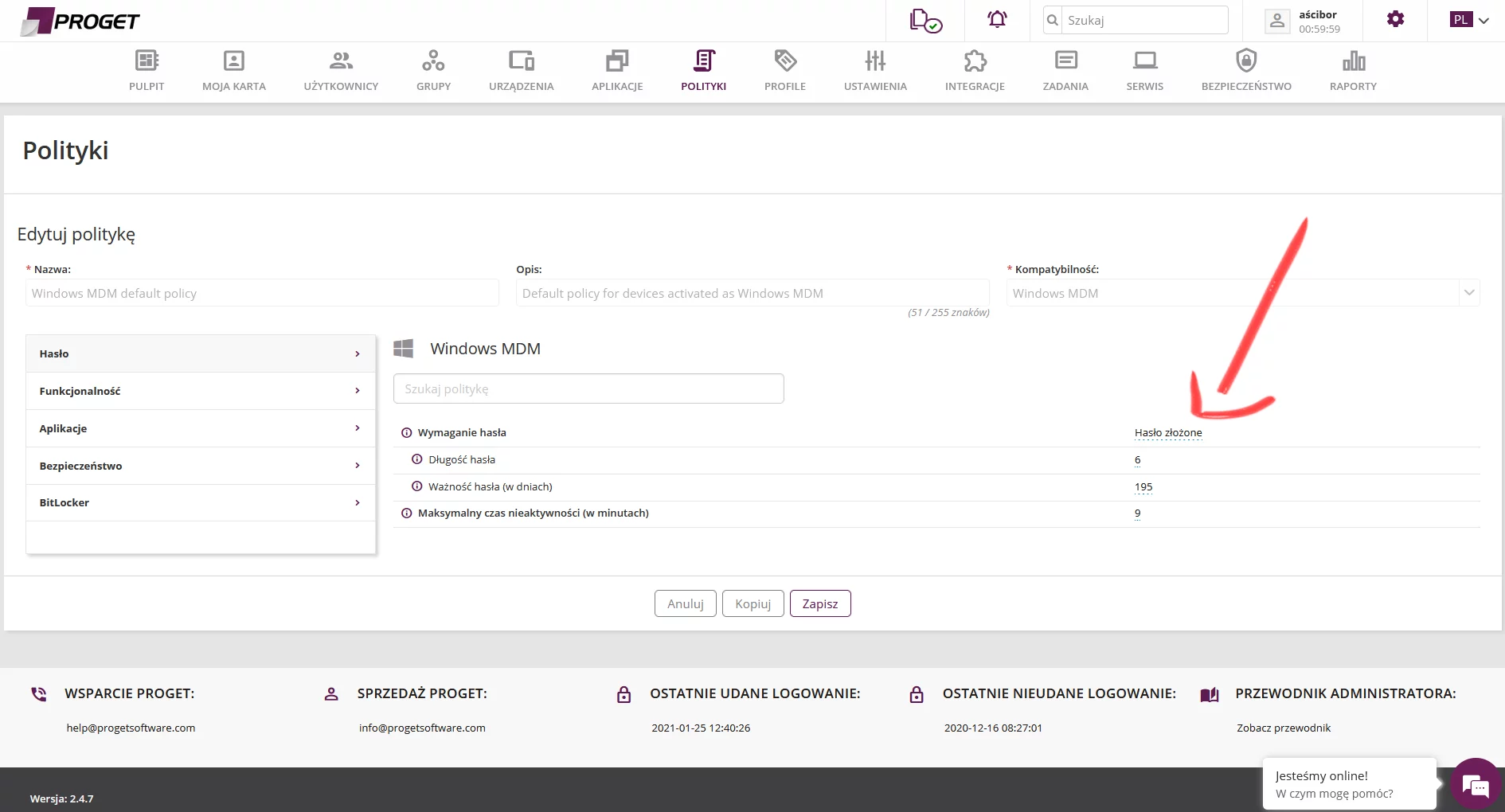
A password is less secure than the alternative login provided by Windows 10, although it will always be better, and should be mandatory than a simple password, such as “2021!@#$”.
Even the strongest password will not matter if it is exposed to a stranger. Therefore, an organization can force the BitLocker disk encryption to run, which will further protect company data against third party access. In this respect, the Proget solution gives great opportunities because it works with and without TPM, and supports encryption for a group of computers managed in Active Directory.
Security of the Android system can be managed at a high level. From password policy to modern login methods such as fingerprint, iris, and face scanning.
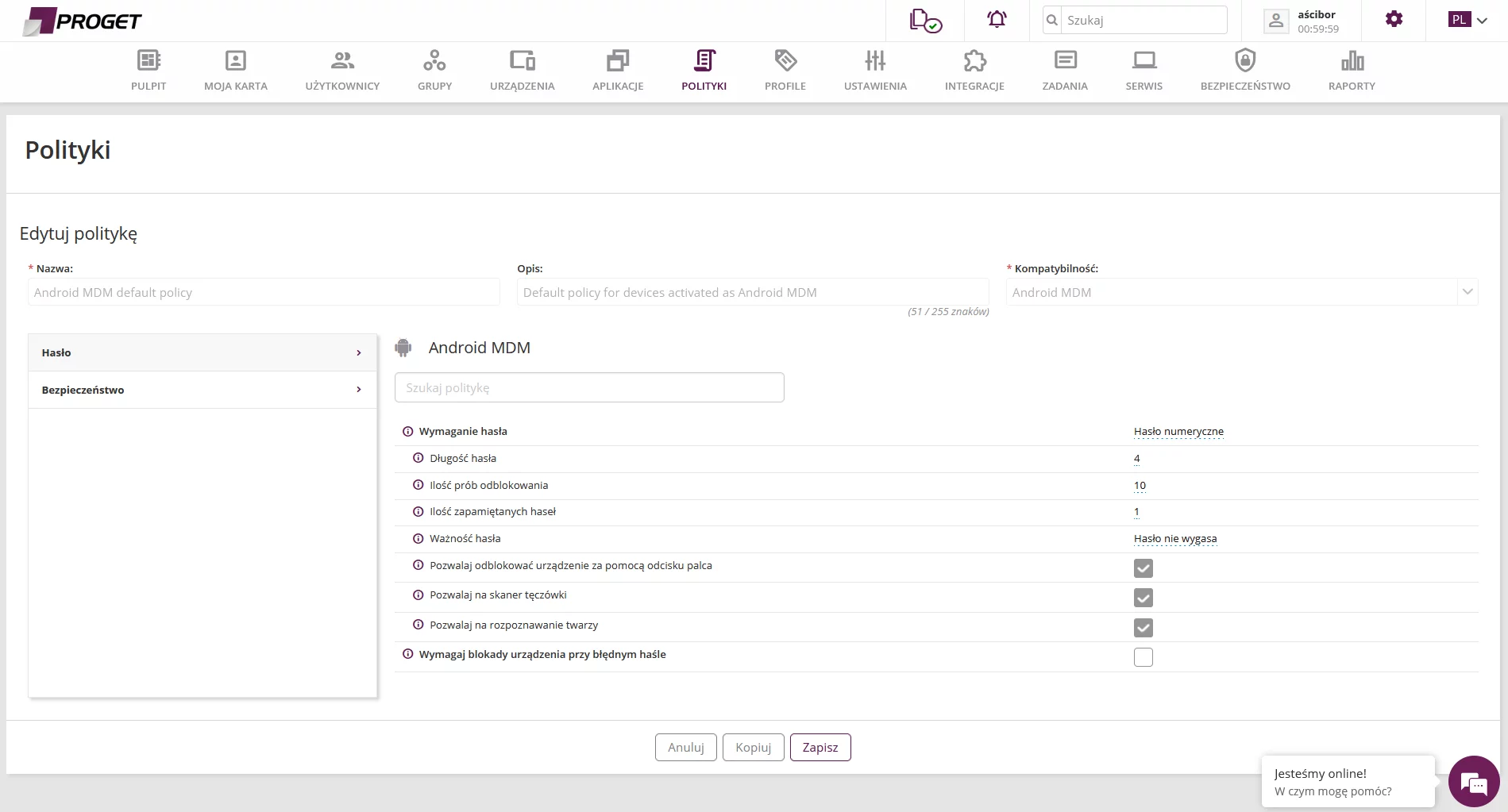
A very nice feature is to delete business data or erase it completely after a selected number of days – unless the device runs out of battery. When it is charged, a smartphone starts the procedure indicated by the administrator (depending on additional settings).
Take the following example: if a smartphone is found discharged after 10 days (number of days can be configured), the device will start erasing data after being charged and switched on. This is a very good solution for the possibility of data breach. The cost of a smartphone is much less severe than revealing secret documents or correspondence.
Configuration policies include Android devices, and those connected to Android Enterprise as part of managed groups of mobile devices. This kind of configuration may include automatic updates of installed applications, prohibition of installing application from “unknown sources”, and denying or allowing data copying between the corporate container and the device.
These settings and more are discovered after getting to know the Proget solution. There are many management scenarios, so it is best to prepare own requirements, and consult them with Proget before implementation.
Ad7. Preventive protection against data breach
Corporate data can be secured indirectly and directly. The latter method takes into account the protection with the security policy level through the following settings:
- Control access to corporate resources through a VPN tunnel
- Based on location, e.g. in the indicated GPS zone.
- By monitoring a device and detecting potential threats to which it may be exposed.
- Through trusted wireless networks that are shared in a corporate environment.
The indirect method is to get clearly separate corporate and personal applications, and to allow only selected applications (white and black lists of smartphone apps) to be used.
Summary
Proget software is a company from Bielsko-Biala, so we are pleased that they have managed to break into foreign markets. We keep our fingers crossed, and wishing them to get new features in their software for Windows and announced version for MacOS.
Installation on devices is not complicated. It is just different. The product positively surprises from the very first moment to then show very rich settings for mobile environments (as opposed to Windows ones which are considered essential). It is a pity that the Patch Management module is missing for Windows. This would improve security management and allow Proget to stabilize its position as a product for Windows environments.
Proget is not an all-in-one solution, and we can hardly expect that it will ever be. As we wrote earlier – it is good that it is not because Proget has found its own niche in a specific market and customer, so it specializes in its class: MAM, EMM, MDM.